Documents obtained by hackers from the Italian spyware manufacturer Hacking Team confirm that the company sells its powerful surveillance technology to countries with dubious human rights records.
Internal emails and financial records show that in the past five years, Hacking Team’s Remote Control System software — which can infect a target’s computer or phone from afar and steal files, read emails, take photos and record conversations — has been sold to government agencies in Ethiopia, Bahrain, Egypt, Kazakhstan, Morocco, Russia, Saudi Arabia, Sudan, Azerbaijan and Turkey. An in-depth analysis of those documents by The Intercept shows Hacking Team’s leadership was, at turns, dismissive of concerns over human rights and privacy; exasperated at the bumbling and technical deficiency of some of its more controversial clients; and explicitly concerned about losing revenue if cut off from such clients.
Hacking Team has an unusually public profile for a purveyor of surreptitious technology, and it has drawn criticism because its malware has shown up on the computers of activists and journalists. Most of the countries identified in the leaked files have previously been connected to Hacking Team by human rights researchers working with computer forensics experts. The company has long denied any implication in human rights abuses, regularly pointing reporters to a policy on its website that says it only sells to governments, investigates allegations of human rights abuses and complies with international blacklists.
But the company has never confirmed its client list, nor has it given an example of an instance in which it cut off a customer because of human rights concerns.
Some 400 gigabytes of emails and documents released by hackers Sunday night show that while the company makes sure to sell only to government users, except in rare cases, the legal use of the technology is left up to those governments to determine.
The emails show that Hacking Team has relied on a biannual analysis of the countries it can legally sell to, conducted by a global law firm, Bird & Bird. The reports, going back to at least 2013, analyze the current restrictions in Italian law under which Hacking Team would be barred from selling its software, Remote Control System, or RCS.
The reports note countries currently under sanctions, and also summarize the concerns of international human rights groups — “not entailing any legal assessment on our part” — for many of Hacking Team’s clients.
Occasionally, the company asks for specific review — in 2013, for example, it asked Bird & Bird to review Bahrain, which has been consistently criticized for human rights offenses since pro-democracy protests began there in 2011. The report found that there were no set restrictions under Italian or international law that would limit exports of RCS to Bahrain. However, it noted that human rights groups and the European Union had, on multiple occasions, observed “policies and actions in violation of human rights and in particular violations of freedom of expression and association.”
Seeing “opportunity” where others see repression
Previous research identified Bahrain as using software made by one of Hacking Team’s prime competitors, FinFisher, to go after Arab Spring activists. When those allegations surfaced in 2012 and FinFisher was in the hot seat, Hacking Team’s account manager sent around the link with a smiley face: “rumor has it, there’s an opportunity in Bahrain…” Indeed, Bahrain’s Ministry of Defense bought RCS in 2013, and remained a client in 2015. The company also appears to have been in talks with the country’s intelligence agency, in partnership with another the surveillance tech provider, the U.S.-Israeli company Nice Systems.
The emails and reports confirm that the company avoids selling to countries under sanction, but is always evaluating possibilities. In a May email, CEO and co-founder David Vincenzetti writes of a potential deal in Libya: “I’m skeptical, it’s a failed state, we can ask for authorization but I really don’t know if it is a blacklisted country.”
Syria, he notes in another email, is one place Hacking Team should break its habit of not commenting on clientele. “Syria is the most vicious, visible and known by the public example of a dictator committing a protracted never ending manslaughter using ignoble tools,” Vincenzetti commented. Nonetheless, emails show that in 2011, before the uprising against Bashar Al-Assad began, the company was still looking for business there.
“The Syrian person from Lattakia telephoned me and I explained our product a bit,” wrote Mostapha Maana, Hacking Team’s account manager for the Middle East, in Italian in April 2011. “He told me that the situation in Syria is calm and advised me to go and see him this week. He said that the product could be very interesting especially after the mess that’s happened lately.”
The company’s first concern when human rights concerns emerge in the press is to reassure others that the technology’s effectiveness has not been affected by the exposure. Hacking Team generally seems to view legal frameworks for the products’ use as the responsibility of the government client. One executive noted that a speech on legal issues would go over well in “Washington or Prague, but I don’t think Arab clients take care of legal issues in using our product.”
On a mailing list that Vincenzetti maintains — commenting on foreign affairs and sharing generally right-wing and hawkish angles on Russia, China and technology news — he refers to privacy advocates and journalists as “ideological hardliners.”
In an email to colleagues responding to a Slate piece last year on spyware, Vincenzetti lamented that “the ‘protect privacy, at_any_cost’ theme is somehow dominant today.”
For “activists working for no-profit organizations … directing their efforts towards small, possibly foreign, technology companies is easy; directing their efforts toward local agencies is hard and risky,” he wrote in another email. “I have a question for you all: PLEASE NAME a single really ‘democratic’ country, a country which does not violate anybody’s rights and has a TOTALLY clean human rights record.”
The emails detail the company’s response to some high-profile allegations of wrongdoing, a few of which are laid out below.
Turkey: All options on the table, until they weren’t
In the summer of 2013, Wired reported that an American citizen had been targeted by what appeared to be Hacking Team software linked to Turkey. At the time, Hacking Team’s U.S. spokesperson Eric Rabe declined to comment on the company’s relationship with Turkish authorities, but in an internal email, the company’s executives discussed meeting with Turkish authorities at a trade show to discuss the allegations.
“The result: no cooperation at all. They categorically deny any involvement in the case. I told our people to insist and to explain them that such media exposures are not beneficial for anybody,” Vincenzetti wrote. “All options are on the table, that is, we could well decide to stop supporting them.”
Vincenzetti does not specify which agency is the client, but the Turkish client in Hacking Team’s records for that year is the Turkish National Police. (Internal emails also show that “Kamel Abed,” whose name had appeared on various appearances of malware, was indeed a name invented by Hacking Team.)
Another email discusses plans to meet with the client in Milan and discuss the incident. Whatever scolding occurred in that meeting, Turkish National Police remained a Hacking Team client as of this year.
Ethiopia: “700k is a relevant sum”
Last year, researchers with the Citizen Lab at the University of Toronto identified traces of Hacking Team spyware on the computers of Ethiopian journalists living in Northern Virginia. Ethiopia’s government is ranked as one of the worst in Africa for press freedom, and regularly targets journalists under anti-terrorism laws.
The researchers believed that the journalists, who worked for Ethiopian Satellite Television (ESAT) — a network run largely by expatriates and seen as close to opposition parties — had been attacked by Ethiopia’s Information Network Security Agency, or INSA. (The Citizen Lab researchers included Morgan Marquis-Boire, First Look Media’s director of security and co-author of this article.) At the time, the Ethiopian government’s spokesperson in Washington denied using Hacking Team’s products, telling the Washington Post that Ethiopia “did not use and has no reason at all to use any spyware or other products provided by Hacking Team or any other vendor inside or outside of Ethiopia.”
Then last March, Citizen Lab again published evidence of Hacking Team’s malware, this time in an attachment to an email sent to Neamin Zeleke, ESAT’s managing director. The Ethiopian spokesperson said the county “acts in compliance with its own laws and with the laws of nations.”
Hacking Team refused to confirm its clients but repeated that the company investigated alleged human rights abuses. However, Rabe told the Washington Post, “It can be quite difficult to determine facts, particularly since we do not operate surveillance systems in the field for our clients.”
Emails and internal records clearly show that the incident set off a debate within the company about whether the bad press and potential exposure of Hacking Team technology was worth it.
“[Citizen Lab] found the source of the attack because these geniuses used the same email address they had used in the previous attack to send the doc with the exploit,” the chief technical author wrote in Italian, referring to the Ethiopian clients. Vincenzetti ordered them to temporarily suspend the account.
But the follow-up investigation appears to have consisted of a terse email to their INSA contact stating, “would you please give a detailed explanation regarding the following allegations?” with links to reports.
INSA’s representative replied that Zeleke was targeted as a member of Ginbot7, an opposition political party that the Ethiopian government declared a terrorist group in 2011. “To us, Nemene Zeleke is one of the top leaders of a terrorist organization, not a journalist,” the INSA agent wrote.
Hacking Team seemed placated, but still irritated. Chief Operating Officer Giancarlo Russo wrote to other executives that it “seems that from a legal point of view they are compliant with their own law.”
Rabe, meanwhile, argued that “the issue is their incompetent use of HT tools. They can argue about whether their target was a justified target or not, but their use of the tool several times from the same email address, and in repeatedly targeting and failing to get access is what caused the exposure of our technology.” (Indeed, emails to Hacking Team’s support system show clients complaining about the leak.)
Daniele Milan, Hacking Team’s operations chief, weighed in favor of closing the account, saying that INSA’s “reckless and clumsy usage of our solution caused us enough damage.”
“But I know that 700k is a relevant sum,” he adds in Italian in another email.
The executives eventually decided to reinstate Ethiopia’s license. In May, after a few weeks’ back-and-forth, the company proposed a new contract with more on-the-ground training and supervision — “additional services” that a business development executive noted could add hundreds of thousands of euros to the country’s bill.
Morocco: A national security ally
Hacking Team emerged in the international press in 2012, when a fake document was used to implant malware on the computers of journalists who were critical of Morocco’s government, at the time facing protests inspired by the Arab Spring. Activists and researchers have long suspected the malware originated with Hacking Team and have continued to work to link the attack to Remote Control System. Just this month, researchers traced malware to IP addresses associated with the Conseil Supérieur de la Défense Nationale, or CSDN, described as a council of Morocco’s various security agencies. (Marquis-Boire was involved in that research.)
As usual, Hacking Team publicly declined to name its clients. The Moroccan government has protested the spying allegations loudly, even filing a lawsuit this spring against activists who prepared a report recounting first-hand experiences of the journalists and activists who had been targeted.
Company emails and business records show that Hacking Team has indeed been selling to the Moroccan government at least since 2010, and still does, using a company called Al Fahad Smart Systems, based in the United Arab Emirates, as a middleman. The invoices reference CSDN as well as the domestic spy agency Direction Générale de la Surveillance du Territoire, or DST. In April of this year, the company was pitching its services to the Royal Moroccan Gendarmerie.
There is no apparent record that the company asked its Moroccan clients about targeting journalists or opposition. When the story about Moroccan journalists first broke in 2012, internal emails among executives stressed that the articles did not definitively show it was Hacking Team’s malware.
Morocco continues to be an important client. Vincenzetti recently sent around a Financial Times article headlined, “Spectre of ISIS used to erode rights in Morocco,” with the comment, “NOT REALLY.”
“The King of Morocco is a benevolent monarch,” Vincenzetti wrote in the email to a few colleagues. “Morocco is actually the most pro-Western Arab country, national security initiatives are solely needed in order to tighten stability.”
“A sandwich vendor” for Sudan
In June 2014, a U.N. panel monitoring the implementation of sanctions on Sudan began asking Hacking Team for information about alleged sales to the government there. Hacking Team ignored the panel’s letter for months. Eventually, in January of this year, when prodded about the inquiry by Italian authorities, Hacking Team embarked on a campaign of evasion.
Internal records show that in 2012, Sudan’s National Intelligence and Security Service in Khartoum paid a total of 960,000 euros for Remote Control System. Emails confirm that Hacking Team cut off the account’s service on November 24, 2014.
During a training session for the Sudan intelligence service in January 2014, a Hacking Team engineer noted that none of the people attending the training “is enough prepared for the product usage. The main problem is the lack of basic computer usage, followed by a complete lack of English: 90% of them had problems just for typing a username on a keyboard and serious difficulties in moving the mouse.”
In November, Russo wrote that Sudan was “unofficially suspended, on-hold.”
“We’re discussing with the [Italian] ministry the limitations on exports to various countries and this is the most sensitive at the moment,” he wrote.
In response to the United Nations panel, the company responded this January that they were not currently selling to Sudan. In a follow-up exchange, Hacking Team asserted that their product was not controlled as a weapon, and so the request was out of the scope of the panel. There was no need for them to disclose previous sales, which they considered confidential business information.
In internal emails, the company debates the mission of the panel. “It looks like their focus is to trace every single armament,” wrote Russo, the chief operating officer. “We absolutely need to avoid being mentioned in these documents.”
A lawyer consulting for Hacking Team insisted that they should argue that the panel had no jurisdiction over them. “If one sells sandwiches to Sudan, he is not subject, as far as my knowledge goes, to the law,” she wrote. “HT should be treated like a sandwich vendor.”
The U.N. disagreed. “The view of the panel is that as such software is ideally suited to support military electronic intelligence (ELINT) operations it may potentially fall under the category of ‘military … equipment’ or ‘assistance’ related to prohibited items,” the secretary wrote in March. “Thus its potential use in targeting any of the belligerents in the Darfur conflict is of interest to the Panel.”
Negotiations with Italian authorities were ongoing throughout the spring, with the U.N. proposing to sign a confidentiality agreement, but by early June, the last emails available, the standoff did not appear to have been resolved.
Italy’s export ban
Last fall, the Italian government abruptly froze all of Hacking Team’s exports, citing human rights concerns. After lobbying Italian officials, the company eventually won back the right to sell its products abroad. But emails connected to the incident show that the company’s reputation for sales to sketchy places has harmed its business, even before this latest leak.
The document, from the Ministry of Economic Development, does not specify a source or specific countries, but states that the ministry had information about Hacking Team’s “possible uses concerning internal repression and violations of human rights.” As a result, it was applying a “catch-all” provision of an export law to block Hacking Team’s products.
Hacking Team quickly deployed all of its top government connections — Italian clientele, internal records show, including the Carabinieri, or military police, and the prime minister’s office — to lobby against the order. They brought pressure to bear from investors and funders, including Milan’s regional government.
The export hold could quickly destroy the company, CEO Vincenzetti warned in an email to Russo, the chief operating officer. “We have about two million in funds, we ‘burn’ about 500k a month. We would need the money for liquidation, not bankruptcy.” Customers could sue for breach of contract, and as the principal individual shareholder, with about 32 percent of the company, his personal assets would be on the line, Vincenzetti wrote.
The company composed two letters that Vincenzetti sent around to influential contacts, “one version more polite, and one a bit more ‘from the gut,’” as one employee described them.
“With determination and perseverance, I have always served the country, and I am certain that my company could be called a flower in the buttonhole of Italy,” Vincenzetti wrote. “I never would expect that our work could be considered somehow suspect; I would never have believed I’d have to explain to 40 employees — who every day deepen their efforts to improve our software, proud to be able to contribute in their own small way to the fight against criminality — that that same country considers their efforts, in sum, lowly instruments of potential danger to the country.”
Emails detail meetings with top military officials, who intervened with the Ministry of Economic Development. The company would soon be regulated under new European Union rules for the Wassenaar Arrangement, an international export-control framework that labels intrusion software like Hacking Team’s as a “dual-use” product, or one that can be put to both military and civil aims. In November, the order was revoked, and negotiations began to give Hacking Team a one-time “global license” for exports to countries that had signed on to the arrangement, rather than the deal-by-deal approvals that the Italian authorities originally proposed.
In the heat of the negotiations, Vincenzetti railed against bureaucrats, activists and others in emotional missives to executives and business confidantes.
“Those who are destroying our company are half men, they are cowards, they are blind, they don’t even live a real life,” he wrote. He suggested the mafia might even be behind the Italian government’s actions. But, he said, “they’ll have to physically kill me to stop me.”
Correction: A sentence in this story originally made erroneous reference to “South Sudan” as a Hacking Team spyware client. The client, in fact, was the Republic of Sudan, sometimes referred to as “North Sudan.” Jul 9, 10:25 am ET
IT’S EVEN WORSE THAN WE THOUGHT.
What we’re seeing right now from Donald Trump is a full-on authoritarian takeover of the U.S. government.
This is not hyperbole.
Court orders are being ignored. MAGA loyalists have been put in charge of the military and federal law enforcement agencies. The Department of Government Efficiency has stripped Congress of its power of the purse. News outlets that challenge Trump have been banished or put under investigation.
Yet far too many are still covering Trump’s assault on democracy like politics as usual, with flattering headlines describing Trump as “unconventional,” “testing the boundaries,” and “aggressively flexing power.”
The Intercept has long covered authoritarian governments, billionaire oligarchs, and backsliding democracies around the world. We understand the challenge we face in Trump and the vital importance of press freedom in defending democracy.
We’re independent of corporate interests. Will you help us?
IT’S BEEN A DEVASTATING year for journalism — the worst in modern U.S. history.
We have a president with utter contempt for truth aggressively using the government’s full powers to dismantle the free press. Corporate news outlets have cowered, becoming accessories in Trump’s project to create a post-truth America. Right-wing billionaires have pounced, buying up media organizations and rebuilding the information environment to their liking.
In this most perilous moment for democracy, The Intercept is fighting back. But to do so effectively, we need to grow.
That’s where you come in. Will you help us expand our reporting capacity in time to hit the ground running in 2026?
We’re independent of corporate interests. Will you help us?

I’M BEN MUESSIG, The Intercept’s editor-in-chief. It’s been a devastating year for journalism — the worst in modern U.S. history.
We have a president with utter contempt for truth aggressively using the government’s full powers to dismantle the free press. Corporate news outlets have cowered, becoming accessories in Trump’s project to create a post-truth America. Right-wing billionaires have pounced, buying up media organizations and rebuilding the information environment to their liking.
In this most perilous moment for democracy, The Intercept is fighting back. But to do so effectively, we need to grow.
That’s where you come in. Will you help us expand our reporting capacity in time to hit the ground running in 2026?
We’re independent of corporate interests. Will you help us?
Latest Stories
Midterms 2026
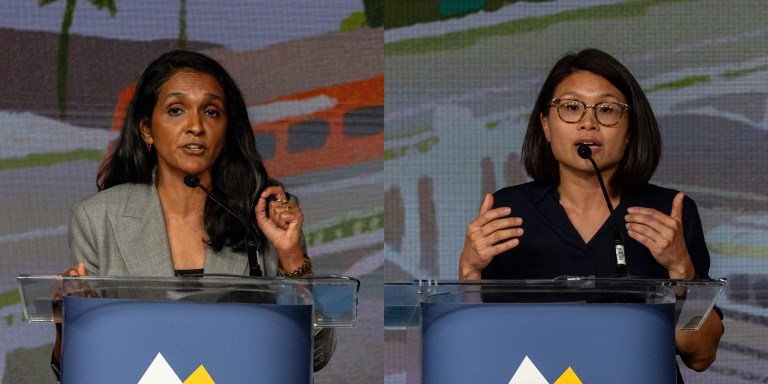
The Los Angeles Left Is at War With Itself Over the Mayor’s Race
Rae Huang supporters say Nithya Raman is compromised. Raman’s base calls Huang a spoiler. Looming over it all: reality TV star Spencer Pratt.

Chilling Dissent
ICE Pepper-Sprayed, Beat Detainees for Protesting “Horrific Conditions” In Delaney Hall Jail
Detainees told a visiting member of Congress that the attacks were “retribution for the ongoing hunger strike.”

Voices
After Uvalde, Texas Stuffed Schools Full of Cops. They Brutalized Students.
Texas’s response to school shootings was as predictable as it was doomed to produce only more violence in schools — violence by cops.
