As of December 1, it is considerably easier for the FBI to hack into computers during investigations.
Thanks to a federal rule change, which passed through several judicial panels before being approved by the U.S. Supreme Court in April, FBI employees can now seek warrants from magistrate judges to remotely access computers even when targets might be outside those judges’ districts, including when the targets’ location is disguised by anonymity software like Tor. Additionally, FBI employees can now search computers infected by malware that makes them part of a botnet — a method used by criminals to disrupt internet service, distribute spam, or spread viruses on a mass scale.
The argument over the modifications, while described by the Department of Justice as simple amendments necessary to facilitate investigations in the modern age, has been contentious.
Privacy advocates like Sen. Ron Wyden, D-Ore., called the impending rule change “one of the biggest mistakes in surveillance policy in years” as he fought on the Senate floor the day before it was scheduled to take effect, joined by colleagues Sens. Chris Coons, D-Del., and Steve Daines, R-Mont. “Law-abiding Americans are going to ask ‘What were you guys thinking?’ when the FBI starts hacking victims of a botnet hack. Or when a mass hack goes awry and breaks their device, or an entire hospital system and puts lives at risk,” he said in a statement.
Just two days prior, security researchers discovered a major software vulnerability in the Firefox and Tor browsers. Before disclosure, users of those browsers were vulnerable to hackers — whether criminals or state actors — who may have been aware of the flaw. The FBI also used an exploit targeted at Firefox in order to ferret out child porn peddlers in an international hacking case over the summer. (Mozilla has issued a patch for the newly discovered bug.)
“On Thursday the FBI gets expanded hacking power,” Chris Soghoian, the ACLU’s chief technologist, tweeted on Tuesday. “Today, someone was caught using malware very similar to the FBI’s code to hack Tor users.”
National security scholars, such as Susan Hennessey, former NSA counsel and current fellow at Brookings Institution, have suggested that the rule changes are minimal and vital — criticizing figures like Wyden for refusing to offer concrete solutions. “Congress decided what to do when they passed the Rules Enabling Act to shift burden to people like Wyden to offer ideas and not obstruction,” she tweeted on Wednesday.
The Justice Department feels the rule changes are needed to investigate crimes, like online distribution of child pornography. If the FBI needed to obtain a warrant from a magistrate judge in order to discover where the offending computer is located, the preexisting standards left them handicapped.
In one recent case involving a massive investigation into the child porn site Playpen, the court tossed out evidence because the agents applied for the warrant outside the district where the computers were located.
Separately, infected botnets are a growing problem; an army of internet-enabled webcams has been wreaking havoc around the world, shutting down popular websites for many hours by flooding the server with traffic.
Assistant Attorney General of the Department of Justice’s Criminal Division Leslie Caldwell has insisted that the “straightforward” changes are several years in the making — and will combat “the dizzying rise of two forms of modern crime: crime committed over the internet by anonymous users … and botnets, or networks of illegally hacked computers that siphon wealth and invade privacy on a massive scale.”
She wrote that the federal changes will not allow the FBI to hack any more computers than it is already allowed to — just change where it can apply for permission. Additionally, she argues, victims’ computers will only be searched for identifying information so the government can notify them of the compromise, to determine the extent of the infection, or to conduct an operation to disrupt that botnet.
Nicholas Weaver, a senior staff researcher at the International Computer Science Institute has written that the actual practice “doesn’t add weaknesses to the systems — in sharp contrast to backdoors,” referring to the FBI’s urgency to mandate technology companies install a way to access encrypted communications. Weaver, though critical of the FBI’s deceptive tactics when requesting warrants from judges to hack computers, says targeted hacking doesn’t pose the same security risks as mandating a security flaw.
However, there’s also a real concern that law enforcement’s use of invasive hacking techniques has not been subject to congressional scrutiny. “Remote computer search rules, which were never debated by Congress, go into effect tomorrow unless stopped,” tweeted Matt Blaze, an associate professor of computer and information science at the University of Pennsylvania.
IT’S EVEN WORSE THAN WE THOUGHT.
What we’re seeing right now from Donald Trump is a full-on authoritarian takeover of the U.S. government.
This is not hyperbole.
Court orders are being ignored. MAGA loyalists have been put in charge of the military and federal law enforcement agencies. The Department of Government Efficiency has stripped Congress of its power of the purse. News outlets that challenge Trump have been banished or put under investigation.
Yet far too many are still covering Trump’s assault on democracy like politics as usual, with flattering headlines describing Trump as “unconventional,” “testing the boundaries,” and “aggressively flexing power.”
The Intercept has long covered authoritarian governments, billionaire oligarchs, and backsliding democracies around the world. We understand the challenge we face in Trump and the vital importance of press freedom in defending democracy.
We’re independent of corporate interests. Will you help us?
IT’S BEEN A DEVASTATING year for journalism — the worst in modern U.S. history.
We have a president with utter contempt for truth aggressively using the government’s full powers to dismantle the free press. Corporate news outlets have cowered, becoming accessories in Trump’s project to create a post-truth America. Right-wing billionaires have pounced, buying up media organizations and rebuilding the information environment to their liking.
In this most perilous moment for democracy, The Intercept is fighting back. But to do so effectively, we need to grow.
That’s where you come in. Will you help us expand our reporting capacity in time to hit the ground running in 2026?
We’re independent of corporate interests. Will you help us?

I’M BEN MUESSIG, The Intercept’s editor-in-chief. It’s been a devastating year for journalism — the worst in modern U.S. history.
We have a president with utter contempt for truth aggressively using the government’s full powers to dismantle the free press. Corporate news outlets have cowered, becoming accessories in Trump’s project to create a post-truth America. Right-wing billionaires have pounced, buying up media organizations and rebuilding the information environment to their liking.
In this most perilous moment for democracy, The Intercept is fighting back. But to do so effectively, we need to grow.
That’s where you come in. Will you help us expand our reporting capacity in time to hit the ground running in 2026?
We’re independent of corporate interests. Will you help us?
Latest Stories

Trials of Richard Glossip
Richard Glossip on Life After Decades on Death Row
In an exclusive interview at home in Oklahoma City, Glossip describes his first days of freedom in a world he hasn’t experienced for nearly 30 years.
Midterms 2026
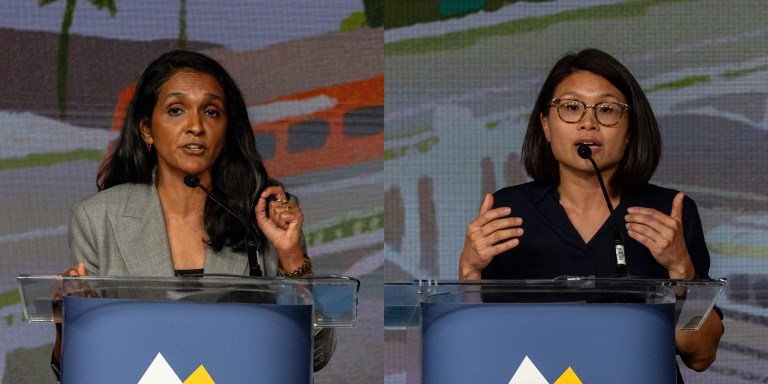
The Los Angeles Left Is at War With Itself Over the Mayor’s Race
Rae Huang supporters say Nithya Raman is compromised. Raman’s base calls Huang a spoiler. Looming over it all: reality TV star Spencer Pratt.

Chilling Dissent
ICE Pepper-Sprayed, Beat Detainees for Protesting “Horrific Conditions” In Delaney Hall Jail
Detainees told a visiting member of Congress that the attacks were “retribution for the ongoing hunger strike.”


