As my colleague Glenn Greenwald told WNYC on Monday, while there may never be conclusive evidence that the Democratic National Committee was hacked by Russian intelligence operatives to extract the trove of embarrassing emails published by WikiLeaks, it would hardly be shocking if that was what happened.
“Governments do spy on each other and do try to influence events in other countries,” Glenn noted. “Certainly the U.S. government has a very long and successful history of doing exactly that.”
Even so, he added, given the ease with which we were misled into war in Iraq by false claims about weapons of mass destruction — and the long history of Russophobia in American politics — it is vital to cast a skeptical eye over whatever evidence is presented to support the claim, made by Hillary Clinton’s aide Robby Mook, that this is all part of a Russian plot to sabotage the Democrats and help Donald Trump win the election.
Clinton campaign manager on DNC leak: Experts say "Russians are releasing these emails" to help Trump #CNNSOTU https://t.co/GwJhloosPs
— CNN Politics (@CNNPolitics) July 24, 2016
The theory gained some traction, particularly among Trump’s detractors, in part because the candidate has seemed obsessed at times with reminding crowds that Russian President Vladimir Putin once said something sort of nice about him (though not, as Trump falsely claims, that the American is “a genius”). Then last week, Trump’s campaign staff watered down a pledge to help Ukraine defend its territory from Russian-backed rebels and the candidate told the New York Times he would not necessarily honor the NATO treaty commitment that requires the United States military to defend other member states from a direct attack by Russia.
Since Trump has refused to release his tax returns, there are also questions about whether or not his businesses might depend to some extent on Russian investors. “Russians make up a pretty disproportionate cross-section of a lot of our assets,” Trump’s son Donald Jr. told a real estate conference in 2008, the Washington Post reported last month. “We see a lot of money pouring in from Russia.”
Paul Manafort, who is directing Trump’s campaign and was for years a close adviser of a Putin ally, former President Viktor Yanukovych of Ukraine, called the theory that Trump’s campaign had ties to the Russian government “absurd.” (On Monday, Michael Isikoff of Yahoo News reported that a DNC researcher looking into Manafort’s ties to pro-Russian politicians in Ukraine in May had been warned that her personal Yahoo email account was under attack. “We strongly suspect that your account has been the target of state-sponsored actors,” the warning from the email service security team read.)
Unhelpfully for Trump, his most senior adviser with knowledge of the world of hacking, retired Lt. Gen. Michael T. Flynn, former director of the Defense Intelligence Agency, told Bloomberg View that he “would not be surprised at all” to learn that Russia was behind the breach of the DNC network. “Both China and Russia have the full capability to do this,” he said.
Later on Monday, Trump himself then attributed the attack on the DNC to “China, Russia, one of our many, many ‘friends,'” who “came in and hacked the hell out of us.”
Since very few of us are cybersecurity experts, and the Iraq debacle is a reminder of how dangerous it can be to put blind faith in experts whose claims might reinforce our own political positions, there is also the question of who we can trust to provide reliable evidence.
One expert in the field, who is well aware of the evidence-gathering capabilities of the U.S. government, is Edward Snowden, the former Central Intelligence Agency technician and National Security Agency whistleblower who exposed the extent of mass surveillance and has been given temporary asylum in Russia.
“If Russia hacked the #DNC, they should be condemned for it,” Snowden wrote on Twitter on Monday, with a link to a 2015 report on the U.S. government’s response to the hacking of Sony Pictures. In that case, he noted, “the FBI presented evidence” for its conclusion that North Korea was responsible for the hacking and subsequent release of internal emails. (The FBI is now investigating the breach of the DNC’s network, which officials told the Daily Beast they first made the committee aware of in April.)
What’s more, Snowden added, the NSA has tools that should make it possible to trace the source of the hack. Even though the Director of National Intelligence usually opposes making such evidence public, he argued, this is a case in which the agency should do so, if only to discourage future attacks.
Evidence that could publicly attribute responsibility for the DNC hack certainly exists at #NSA, but DNI traditionally objects to sharing.
— Edward Snowden (@Snowden) July 25, 2016
Without a credible threat that USG can and will use #NSA capabilities to publicly attribute responsibility, such hacks will become common.
— Edward Snowden (@Snowden) July 25, 2016
To summarize: the US Intel Community should modernize their position on disclosure. Defensive capabilities should be aggressively public.
— Edward Snowden (@Snowden) July 25, 2016
Another former insider with knowledge of American and Russian intelligence capabilities, Michael McFaul, the U.S. ambassador to Russia from 2012 to 2014, agreed that it should be possible for the U.S. to present proof if Russia was, in fact, responsible for the attack.
I assume that the US counterintelligence agencies have been investigating Russian theft of DNC emails. Hope they tell us results soon.
— Michael McFaul (@McFaul) July 24, 2016
As U.S. voter, I'm appalled by Russian meddling, want it investigated & stopped. As long-time analyst of Russia, Im impressed; they're good
— Michael McFaul (@McFaul) July 24, 2016
While we wait to see if the NSA will take its most famous former employee’s advice, it is worth reading a thorough review of the evidence produced so far, compiled for Motherboard by Thomas Rid, a professor at King’s College London who has charted the use of hacking for espionage.
As Rid explains, the attribution of the DNC hack to Russian intelligence agents was first suggested on June 15 by CrowdStrike, the cybersecurity firm hired by the Democrats to investigate the possible breach of their system in May.
Last month, one of the firm’s founders, Dmitri Alperovitch, explained in a detailed technical analysis of their findings that CrowdStrike discovered “two separate Russian intelligence-affiliated adversaries present in the DNC network in May.”
The groups, he added, are so familiar to the investigators from previous attacks that they have acquired commonly used nicknames in the security industry. One, “Cozy Bear” or “APT 29,” had been inside the committee’s network for about a year; a second, “Fancy Bear,” also called “APT 28,” breached the system in April.
We’ve had lots of experience with both of these actors attempting to target our customers in the past and know them well. In fact, our team considers them some of the best adversaries out of all the numerous nation-state, criminal and hacktivist/terrorist groups we encounter on a daily basis. Their tradecraft is superb, operational security second to none and the extensive usage of “living-off-the-land” techniques enables them to easily bypass many security solutions they encounter. In particular, we identified advanced methods consistent with nation-state level capabilities including deliberate targeting and “access management” tradecraft — both groups were constantly going back into the environment to change out their implants, modify persistent methods, move to new Command & Control channels and perform other tasks to try to stay ahead of being detected.
Cozy Bear is the group that “successfully infiltrated the unclassified networks of the White House, State Department, and U.S. Joint Chiefs of Staff” last year, Alperovitch noted. Fancy Bear, he added, has “been linked publicly to intrusions into the German Bundestag and France’s TV5 Monde TV station in April 2015.”
Readers with a high level of technical competence can parse the clues explained fully in Alperovitch’s blog post, but he also noted a surprising fact: that the two groups thought to be affiliated with rival Russian intelligence agencies — the successor to the Soviet-era KGB, known as the FSB, and the GRU, a military intelligence service — appeared unaware of each other’s activities.
“We have identified no collaboration between the two actors, or even an awareness of one by the other,” Alperovitch observed. “Instead, we observed the two Russian espionage groups compromise the same systems and engage separately in the theft of identical credentials.”
One day after this initial attribution of the attack to Russian intelligence was made public by CrowdStrike and the DNC, someone using the pseudonym Guccifer 2.0, in reference to the Romanian hacker who famously uncovered George W. Bush’s secret career as a painter of selfies, started publishing documents stolen from the committee’s servers on a WordPress blog set up that day, and taunting the security experts on Twitter.
Guccifer 2.0, who claims to be a Romanian who dislikes Russians, told my colleague Sam Biddle that he or she had carried out the attack with no help from anyone else, just to expose “all those illuminati that captured our world,” and had provided hacked documents to WikiLeaks.
However, several analysts pointed out that there is evidence in the metadata that copies of the DNC documents posted online by Guccifer 2.0, starting with an opposition research dossier on Trump, appear to have been processed on a computer with Russian language settings. Parsing the documents on Twitter, the blogger Davi Ottenheimer and an information security analyst who writes as @pwnallthethings pointed out that copies of the stolen documents uploaded to WordPress rendered the hacker’s username, Iron Felix, in Cyrillic characters, and gave error messages for links in Russian.
https://twitter.com/pwnallthethings/status/743197064843104257
"error! invalid hyperlinks" in Russian… pic.twitter.com/T9jmLnNiKF
— davi (((?))) ?? (@daviottenheimer) June 15, 2016
Doubts were also cast over Guccifer 2.0’s identity by his or her apparent lack of fluency in Romanian in an online chat with Lorenzo Franceschi-Bicchierai of Motherboard.
Despite Guccifer 2.0’s claims, CrowdStrike’s attribution to the previously known Russian groups was supported by subsequent research last month from two rival network security firms: Fidelis Cybersecurity and Mandiant.
“We performed an independent review of the malware and other data (filenames, file sizes, IP addresses) in order to validate and provide our perspective on the reporting done by CrowdStrike,” Michael Buratowski, a Fidelis senior vice president, explained in a detailed technical analysis. The firm’s conclusions supported the attribution to the two well-known Russian groups. Among other factors, Buratowski noted, “the malware samples were conspicuously large” and “contained all or most of their embedded dependencies and functional code.”
“This is a very specific modus operandi less sophisticated actors do not employ,” he argued.
A Mandiant researcher, Marshall Heilman, told the Washington Post he agreed that the malware and associated servers were consistent with those previously used by the two Russian groups.
Another American cybersecurity firm, ThreatConnect, reported on Tuesday that it had uncovered evidence that “Guccifer 2.0 is using the Russia-based Elite VPN service to communicate and leak documents” to reporters.
The suspicion that the raid of the DNC servers might have been carried out by Russian intelligence was unsurprising to some experts, as Wired’s Andy Greenberg reported, given that the FBI warned both Barack Obama and John McCain in 2008 that their campaign computer systems had been breached by foreign hackers, most likely from Russia or China.
Some observers, like the Harvard Law professor Jack Goldsmith, who worked for President George W. Bush, suggested that such attacks might be seen as payback, given that American intelligence agencies have made aggressive use of hacking, which “almost certainly extends to political organizations in adversary states.”
7/ Current U.S. cyber-espionage almost certainly extends to political organizations in adversary states.
— Jack Goldsmith (@jacklgoldsmith) July 26, 2016
As the journalist Marcy Wheeler noted on her blog, according to report on the Snowden documents by Jens Glüsing, Laura Poitras, Marcel Rosenbach and Holger Stark for Spiegel, the NSA hacked into “a key mail server in the Mexican Presidencia domain within the Mexican Presidential network,” during that country’s 2012 election campaign, and intercepted 85,489 text messages sent by the ruling party candidate, Enrique Peña Nieto himself, or his associates.
What makes the DNC breach new, however, is the fact that close to 20,000 emails and other documents — including personal information and credit card details of donors — were provided to WikiLeaks, which made them public on the eve of this week’s convention. Some of the private email traffic made public, which validated complaints from the Bernie Sanders campaign that the DNC officials favored Hillary Clinton, helped to reopen wounds from the bruising primary campaign.
Chants of "WikiLeaks" and "Lock her up" outside the DNC convention. pic.twitter.com/YksSfoWnKn
— Philip Crowther (@PhilipinDC) July 25, 2016
https://twitter.com/jbarro/status/757679402780065792
The role played by WikiLeaks, and the professed indifference of the group’s founder, Julian Assange, to the source of the hacked documents, caused some journalists to ask if the site had allowed itself to be used as part of a post-modern dirty trick, a sort of Watergate 2.0.
One reporter, James Surowiecki of the New Yorker, even mused about how WikiLeaks might have treated documents provided by the Watergate burglars had it been around in 1972 when the Republican operatives broke into the DNC office in that building, precisely to obtain damaging information about the party through theft and surveillance.
If WL had been around in '72, would it have published DNC documents Watergate burglars stole and transcripts from the bugs they planted?
— James Surowiecki (@JamesSurowiecki) July 24, 2016
Of course, many other reporters have taken the view that the material made public by WikiLeaks is clearly newsworthy, given that it helps expose the inner workings of a largely unaccountable private political party, which plays a central and privileged role in the election of America’s leaders. That is why an array of publications, including The Intercept, quickly started to provide reporting and analysis on what was revealed in the leaked documents.
Asked by NBC News on Monday if WikiLeaks might have been used to distribute documents stolen as part of a Russian intelligence operation, Assange insisted there was “no proof of that whatsoever — we have not disclosed our source, and of course this is a diversion that’s being pushed by the Hillary Clinton campaign.”
WATCH: No proof Russians used WikiLeaks in #DNCLeak, Julian Assange tells @RichardEngel on @NBCNightlyNews. https://t.co/UJCBe4fT9l
— NBC Nightly News with Lester Holt (@NBCNightlyNews) July 25, 2016
Of course, given that a cornerstone of the WikiLeaks promise to sources is that the site was designed to receive material without revealing the identity of the leaker to anyone at the anti-secrecy group, it should be impossible for Assange himself to know that the hacked DNC documents did not come from a Russian intelligence operative — or, for that matter, a Republican one.
Convinced by the available evidence that the leak was orchestrated by Russian intelligence, Thomas Rid, the security analyst who writes for Motherboard, went so far as to suggest that by publishing these documents, WikiLeaks had become “a legitimate target” for counterintelligence operations by the five-nation club of the United States, Britain, Canada, Australia, and New Zealand.
https://twitter.com/RidT/status/757153240458858496
Although WikiLeaks describes the hacked DNC emails as “part one of our new Hillary Leaks series,” Assange himself rejected the charge that he is helping in a partisan attack. “This is a quite a classical release,” he told Amy Goodman of “Democracy Now” on Monday, “showing the benefit of producing pristine data sets, presenting them before the public, where there’s equal access to all journalists and to interested members of the public to mine through them and have them in a citable form where they can then be used to prop up certain criticisms or political arguments.”
Assange demurred when Goodman asked if he preferred Trump over Clinton — “You’re asking me, do I prefer cholera or gonorrhea?” — but he was more forthright in an interview with Robert Peston of Britain’s ITV on June 12, two days before the DNC hack was first reported.
After telling Peston in that conversation, “We have emails relating to Hillary Clinton which are pending publication,” Assange was asked if his intention was to help Trump get elected. “Well, I think Trump is a completely unpredictable phenomenon. You can’t predict what he would do in office,” he replied. “From my personal perspective, well, you know, the emails we published show that Hillary Clinton is receiving constant updates about my personal situation; she has pushed for the prosecution of WikiLeaks, which is still in train. So, we do see her as a bit of a problem, for freedom of the press more generally.”
On Twitter, WikiLeaks has been more forthright about seeing the DNC emails and those from Clinton’s personal server — which the group copied from the State Department’s website to make into a searchable database — as material that can be used “to prop up certain criticisms” of the former secretary of state.
Hillary Clinton's showy rewarding of corruption by DWS is an ill wind for the corruption-overton-window of a future presidency.
— WikiLeaks (@wikileaks) July 24, 2016
Audience at DNC turns on Bernie Sanders after he says "we must elect Hillary Clinton" following #DNCLeak https://t.co/yJszgko2XK #DNCinPHL
— WikiLeaks (@wikileaks) July 25, 2016
Some of that criticism, however, has not been well-grounded in fact, leaving the organization open to accusations that, rather than serving as an impartial clearinghouse for leaks, annotated by its readers — like Wikipedia — it has evolved into a platform for analysis by a small circle of insiders.
To take one example, on Saturday, a WikiLeaks tweet incorrectly claimed that one email from the leak revealed that Luis Miranda, the DNC communications director, had suggested that Trump might have been right to say that Ted Cruz’s father was involved in the Kennedy assassination.
#DNCLeak: Trump may be right about Ted Cruz's father & JFK kill — Comms head Luis Miranda https://t.co/jjJV1ndJzM pic.twitter.com/UGbPNLutAE
— WikiLeaks (@wikileaks) July 23, 2016
Reading the email itself, however, shows something quite different. The complete text of the email chain makes it clear that Miranda was contributing to a thread in which officials worked together to edit a draft of a humorous press release, or “hit,” that mocked Trump for making such an outlandish suggestion.
While Miranda did write to his colleagues that Cruz’s father might have been part of an anti-Castro Cuban exile community “with questionable histories,” he also indicated that he approved the final text, which was posted online by the DNC that same day. That text put Trump’s claim about Cruz’s father at the top of a list of examples of “the GOP’s presumptive standard bearer just spouting nonsense he reads on the internet or in the tabloids.”
Here's the May 3 DNC press release mocking Trump for discussing conspiracy theories, like Cruz's father killing JFK pic.twitter.com/hiDBXO75hH
— Robert Mackey (@RobertMackey) July 26, 2016
While such errors in the annotation of the DNC documents look more like sloppiness than an attempt to intentionally mislead readers, the mistakes point to a weakness in the platform’s development — the lack of a robust system for correcting mistakes noted by readers, like the one used by Wikipedia.
That problem has also been noted in the way WikiLeaks presented emails from Hillary Clinton’s private server first released by the State Department.
In March, WikiLeaks was criticized by some Twitter followers — including David Kenner, the Middle East editor of Foreign Policy — for the confusing way it presented the text of a draft opinion article sent to Clinton by a friend as if it were the text of an email from her — and one that revealed her secret plan to destroy the Syrian government to help Israel.
Hillary Emails: Overthrow #Syrian government to help Israel https://t.co/e93JddH9nv #syria #iran #saudi pic.twitter.com/yZysFuOT2H
— WikiLeaks (@wikileaks) March 18, 2016
In fact, as the State Department’s website makes clear, that text was sent to Clinton as an attachment to a 2012 email from James Rubin, who served in Bill Clinton’s administration. Reading the email, Rubin attached his draft piece to make it clear that he hoped his essay — which was later published in slightly revised form by Foreign Policy — would convince the Obama administration to help Syrian rebels topple Bashar al-Assad largely to “forestall the biggest danger on the horizon, that Israel launches a surprise attack on Iran’s nuclear facilities.”
Rubin also made it clear in his email that he did not think Clinton shared his view of the situation at that time. “I know you may not agree,” he wrote, “but I thought it was better to share this with you first as at least a new way to look at the problem.”
Unfortunately, the way WikiLeaks described Rubin’s draft op-ed as one of “Hillary Emails” sowed confusion online and led to outraged blog posts and Russian news reports that mistakenly credited Assange’s group with revealing the text of a bombshell email from Clinton that offered insight into her thinking.
Despite concerns that the group’s own annotation of documents related to Clinton might be at times muddled, in his “Democracy Now” interview, Assange defended his decision not to “establish partnerships with the New York Times or the Washington Post,” as he has done in the past to ensure that leaked documents would come to light not only in raw form but also accompanied by some analysis from political or national security reporters.
Working with the editorial staffs of those newspapers on material like this “might be counterproductive,” Assange said, “because they are partisans of one group or another.”
IT’S EVEN WORSE THAN WE THOUGHT.
What we’re seeing right now from Donald Trump is a full-on authoritarian takeover of the U.S. government.
This is not hyperbole.
Court orders are being ignored. MAGA loyalists have been put in charge of the military and federal law enforcement agencies. The Department of Government Efficiency has stripped Congress of its power of the purse. News outlets that challenge Trump have been banished or put under investigation.
Yet far too many are still covering Trump’s assault on democracy like politics as usual, with flattering headlines describing Trump as “unconventional,” “testing the boundaries,” and “aggressively flexing power.”
The Intercept has long covered authoritarian governments, billionaire oligarchs, and backsliding democracies around the world. We understand the challenge we face in Trump and the vital importance of press freedom in defending democracy.
We’re independent of corporate interests. Will you help us?
IT’S BEEN A DEVASTATING year for journalism — the worst in modern U.S. history.
We have a president with utter contempt for truth aggressively using the government’s full powers to dismantle the free press. Corporate news outlets have cowered, becoming accessories in Trump’s project to create a post-truth America. Right-wing billionaires have pounced, buying up media organizations and rebuilding the information environment to their liking.
In this most perilous moment for democracy, The Intercept is fighting back. But to do so effectively, we need to grow.
That’s where you come in. Will you help us expand our reporting capacity in time to hit the ground running in 2026?
We’re independent of corporate interests. Will you help us?

I’M BEN MUESSIG, The Intercept’s editor-in-chief. It’s been a devastating year for journalism — the worst in modern U.S. history.
We have a president with utter contempt for truth aggressively using the government’s full powers to dismantle the free press. Corporate news outlets have cowered, becoming accessories in Trump’s project to create a post-truth America. Right-wing billionaires have pounced, buying up media organizations and rebuilding the information environment to their liking.
In this most perilous moment for democracy, The Intercept is fighting back. But to do so effectively, we need to grow.
That’s where you come in. Will you help us expand our reporting capacity in time to hit the ground running in 2026?
We’re independent of corporate interests. Will you help us?
Latest Stories

Anthropic Says We Must Stop Authoritarian AI. But What About Its Authoritarian Investors?
Anthropic wants to keep AI away from repressive regimes. But what about its part-owner, the repressive dictatorship of Abu Dhabi?
The Intercept Briefing
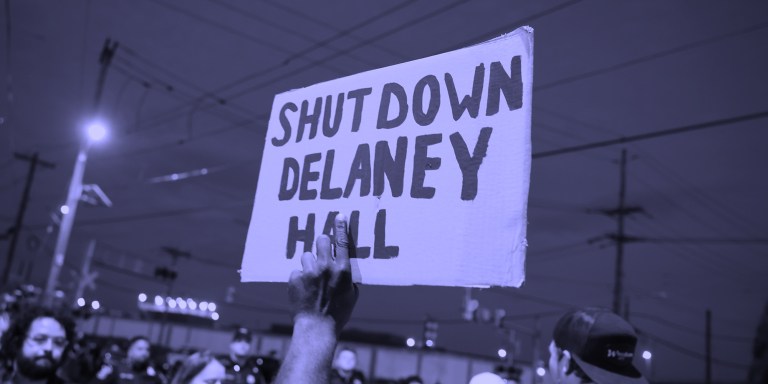
“Warehousing Human Beings”
Former immigration judge Andrea Sáenz and American Immigration Council’s Aaron Reichlin-Melnick on the conditions at Delaney Hall and other ICE detention centers across the U.S.

Trump Administration Tries to Shift Blame for Ebola Response
After cutting its support for frontline healthcare workers in Central Africa, the Trump administration is pointing fingers.





