To date, the only public evidence that the Russian government was responsible for hacks of the DNC and key Democratic figures has been circumstantial and far short of conclusive, courtesy of private research firms with a financial stake in such claims. Multiple federal agencies now claim certainty about the Kremlin connection, but they have yet to make public the basis for their beliefs.
Now, a never-before-published top-secret document provided by whistleblower Edward Snowden suggests the NSA has a way of collecting evidence of Russian hacks, because the agency tracked a similar hack before in the case of a prominent Russian journalist, who was also a U.S. citizen.
People hold pictures of Russian journalist Anna Politkovskaya during a rally in central Moscow on Oct. 7, 2007.

Russian Federal Intelligence Services (probably FSB) are known to have targeted the webmail account of the murdered Russian journalist Anna Politkovskaya. On 5 December 2005, RFIS initiated an attack against the account annapolitkovskaia@US Provider1, deploying malicious software which is not available in the public domain. It is not known whether this attack is in any way associated with the death of the journalist.
Although the NSA document does not specify the account, Anna Politkovskaya was known to use the email address annapolitkovskaia@yahoo.com.
In response to a query from The Intercept about the hacking of Politkovskaya’s account, Yahoo replied in a statement: “We can only disclose information about a specific user account pursuant to our terms of service, privacy policy and law enforcement guidelines.”
The year after her email was hacked, Politkovskaya was murdered, a crime that was widely suspected, though never proven, to be a Kremlin reprisal for her reporting on Chechnya and criticism of Vladimir Putin.
This hack sounds more or less like a very rough sketch of what private firms like CrowdStrike allege the FSB perpetrated against the DNC this year, and presumably what entities like the Federal Bureau of Investigation, the Central Intelligence Agency, and the Office of the Director of National Intelligence have, behind closed doors, told President Obama took place.
What’s particularly interesting here is the provenance of NSA’s claims: The section is classified TS/SI, meaning Top Secret Signals Intelligence, the interception of signals (broadly construed) as they pass from one point to another, including anything from tapped phone calls to monitored internet traffic. That is to say, the NSA knew Russia hacked Politkovskaya because the NSA was spying. Thanks to the Snowden revelations, we know there are many powerful, overlapping government spy programs that could allow the NSA to observe communications as they unfold.
Unfortunately, in the case of this wiki there’s no indication of exactly what sort of SIGINT was collected with regard to Politkovskaya, or how it incriminated Russian intelligence — all we have is the allusion to the evidence, not the evidence. The NSA declined to comment.
But that this evidence existed at all is important, and more so today than ever. Simply, the public evidence that the Russian government hacked the Democrats isn’t convincing. Too much of what’s been passed off to the public as proof of Kremlin involvement is based on vague clues and educated guesses of what took place. Signals intelligence could bridge the empirical gap.
Adm. Mike Rogers, the current NSA chief, has already publicly claimed that Russia was behind the attack. “This was a conscious effort by a nation state to attempt to achieve a specific effect,” Rogers said in November, without specifically mentioning Russia.
NSA whistleblowers have so far given the best idea of what the NSA’s signals intelligence on Russia, today or in 2005, could look like. Earlier this year, Snowden tweeted that if the Russian government was indeed behind the hacking of the Democrats, the NSA most likely has the goods, noting that XKEYSCORE, a sort of global SIGINT search engine, “makes following exfiltrated data easy. I did this personally against Chinese ops.” Snowden went so far as to say that nailing down this sort of SIGINT hacker attribution “is the only case in which mass surveillance has actually proven effective.”
The ex-U.S. intelligence personnel who comprise the group Veteran Intelligence Professionals for Sanity, including fellow high-profile NSA whistleblower William Binney, echoed Snowden’s assessment earlier this month:
The bottom line is that the NSA would know where and how any “hacked” emails from the DNC, HRC or any other servers were routed through the network. This process can sometimes require a closer look into the routing to sort out intermediate clients, but in the end sender and recipient can be traced across the network.
Signal interception can take many different forms, and again, there’s no way to know exactly what the NSA had intercepted surrounding Anna Politkovskaya. But we know intelligence is being gathered on a fine enough level to pin the breach of a single inbox on the Russian government. If the NSA could use signals intelligence to track a specific hack of an American email account in 2005, it’s not too much to assume that, 10 years later, the agency possesses the same or better capability. And signals intelligence is the type of evidence that the American people are owed from the federal government today, as we contemplate a possible confrontation with Russia for interfering in our most important of democratic processes.
IT’S EVEN WORSE THAN WE THOUGHT.
What we’re seeing right now from Donald Trump is a full-on authoritarian takeover of the U.S. government.
This is not hyperbole.
Court orders are being ignored. MAGA loyalists have been put in charge of the military and federal law enforcement agencies. The Department of Government Efficiency has stripped Congress of its power of the purse. News outlets that challenge Trump have been banished or put under investigation.
Yet far too many are still covering Trump’s assault on democracy like politics as usual, with flattering headlines describing Trump as “unconventional,” “testing the boundaries,” and “aggressively flexing power.”
The Intercept has long covered authoritarian governments, billionaire oligarchs, and backsliding democracies around the world. We understand the challenge we face in Trump and the vital importance of press freedom in defending democracy.
We’re independent of corporate interests. Will you help us?
IT’S BEEN A DEVASTATING year for journalism — the worst in modern U.S. history.
We have a president with utter contempt for truth aggressively using the government’s full powers to dismantle the free press. Corporate news outlets have cowered, becoming accessories in Trump’s project to create a post-truth America. Right-wing billionaires have pounced, buying up media organizations and rebuilding the information environment to their liking.
In this most perilous moment for democracy, The Intercept is fighting back. But to do so effectively, we need to grow.
That’s where you come in. Will you help us expand our reporting capacity in time to hit the ground running in 2026?
We’re independent of corporate interests. Will you help us?

I’M BEN MUESSIG, The Intercept’s editor-in-chief. It’s been a devastating year for journalism — the worst in modern U.S. history.
We have a president with utter contempt for truth aggressively using the government’s full powers to dismantle the free press. Corporate news outlets have cowered, becoming accessories in Trump’s project to create a post-truth America. Right-wing billionaires have pounced, buying up media organizations and rebuilding the information environment to their liking.
In this most perilous moment for democracy, The Intercept is fighting back. But to do so effectively, we need to grow.
That’s where you come in. Will you help us expand our reporting capacity in time to hit the ground running in 2026?
We’re independent of corporate interests. Will you help us?
Latest Stories

Israel’s War on Gaza
A Gay Palestinian Fled to Israel’s “Safe Haven.” Israel Tried to Exploit Him for Intelligence.
Israel bills itself as a haven for LGBTQ+ rights. Its bureaucratic system can further endanger queer Palestinian asylum-seekers.

Trials of Richard Glossip
Richard Glossip on Life After Decades on Death Row
In an exclusive interview at home in Oklahoma City, Glossip describes his first days of freedom in a world he hasn’t experienced for nearly 30 years.
Midterms 2026
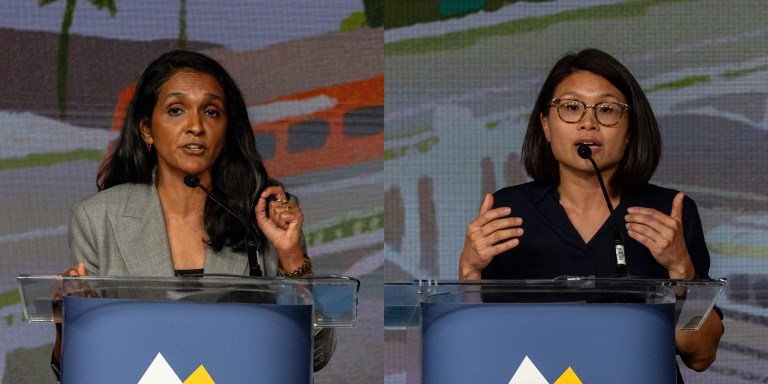
The Los Angeles Left Is at War With Itself Over the Mayor’s Race
Rae Huang supporters say Nithya Raman is compromised. Raman’s base calls Huang a spoiler. Looming over it all: reality TV star Spencer Pratt.




