In early 2018, former National Security Agency chief Keith Alexander worked out a deal with Saudi Crown Prince Mohammed bin Salman and the cyber institute led by one of his closest aides, Saud al-Qahtani, to help the Saudi ruler train the next generation of Saudi hackers to take on the kingdom’s enemies.
While the agreement between IronNet, founded by Alexander, and the cyber school was widely reported in intelligence industry outlets and the Saudi press at the time, it faced no scrutiny for its association with Qahtani, after the brutal killing of Jamal Khashoggi he reportedly orchestrated just a few months later.
Alexander officially inked the deal with the Prince Mohammed bin Salman College of Cyber Security, Artificial Intelligence, and Advanced Technologies — a school set up to train Saudi cyber intelligence agents — at a signing ceremony in Washington, D.C., according to an announcement in early July.
Qahtani’s proxy at the signing noted in a statement that “the strategic agreement will ensure [Saudi Arabia is] benefiting from the experience of an advisory team comprising senior officers who had held senior positions in the Cyber Command of the US Department of Defense.” Alexander’s for-profit cyber security firm IronNet would work closely with the Saudi Federation of Cybersecurity, Programming, and Drones, an affiliate of the college devoted to offensive cyber operations and at the time overseen by Qahtani.
Saudi Arabia’s agreement with IronNet was part of a host of moves to step up its cyber capabilities, coinciding with a campaign against the kingdom’s critics abroad. Khashoggi, then a Washington Post columnist and prominent Salman critic, received a series of threatening messages, including one from Qahtani, warning him to remain silent. Khashoggi, whose family and close associates discovered listening malware electronically implanted on their smartphones, was then lured to the Saudi Embassy in Istanbul.
It was there that a team dispatched by Qahtani detained and tortured the Saudi government critic. Qahtani, according to reports, beamed in through Skype to insult Khashoggi during the ordeal, allegedly instructing his team to “bring me the head of the dog.” Khashoggi was then dismembered with a bone saw.
IronNet’s agreement tied to the alleged mastermind behind the killing of Khashoggi is not listed on the IronNet website, and it is not known if the business relationship still stands — or what the extent of it ever was. IronNet and representatives of the Saudi government did not respond to repeated requests for comment. The Saudi relationship, according to former IronNet employees, has largely been shrouded in secrecy, even within the firm.
Qahtani’s role of enforcer on behalf of bin Salman, well known prior to the Khashoggi slaying, has closely followed the young prince’s meteoric rise as the effective leader of Saudi Arabia.
In 2017, Qahtani played a pivotal role in the abduction and interrogation of hundreds of Saudi elites, who were held captive at the Ritz-Carlton in Riyadh, at which they were forced to pledge loyalty and money to Salman. Qahtani personally led the questioning efforts, according to reports.
Later that year, he reportedly participated in the interrogation of former Lebanese Prime Minister Saad al-Hariri, who was beaten and forced to resign. The following year, according to the brother of Saudi women’s rights activist Loujain al-Hathloul, Qahtani also directly participated in the torture of al-Hathloul, where he mocked her and threatened to have her raped.
On behalf of the kingdom, Qahtani has made it his personal quest to acquire and expand Saudi cyberwarfare tools. Beyond the deal with IronNet and other top-flight American cyber experts, he has spent over a decade directly negotiating the accumulation of computer and phone infiltration technology.
Qahtani took the helm of official state-backed efforts to expand Saudi Arabia’s cyber offensive capabilities in October 2017, when he was named president of a committee called the Electronic Security and Software Alliance, later renamed the Saudi Federation for Cybersecurity, Programming, and Drones.
Earlier this year, SAFCSP signed an agreement with Spire Solutions, a consulting firm that partners with a wide range of cyber intelligence contractors. Haboob, another cyber venture promoted by Qahtani, is a private venture that recruits hackers on behalf of the Saudi government. Haboob’s chair, Naif bin Lubdah, is on SAFCSP’s board of directors.
In 2018, Chiron Technology Services, another American cyber consulting firm, also inked a memorandum of understanding to provide training to the same Saudi hacker school advised by IronNet. Chiron’s team includes top talent recruited from the U.S. Air Force, Army, and NSA, including Michael Tessler, who previously worked at the NSA’s Tailored Access Operations command, which handles high-profile computer infiltration missions of foreign governments.
Jeff Weaver, the chief executive of Chiron, said in an email that his company signed a memorandum of understanding “with the college to develop a cybersecurity curriculum in support of their technical degree programs. However, no collaboration ever occurred, and they never called on us to contribute. We haven’t heard from them since 2018.”
Online cyber sleuths identified Qahtani’s multiple handles on online hacking forums, where he was an active member seeking to purchase hacking tools. A screen name used by Qahtani, for instance, appeared to have purchased a remote access trojan known as Blackshades, which can infect targeted computers to modify and seize files, activate the webcam, and record keystrokes and passwords.
Cybersecurity researchers have identified powerful hacking technology implanted on the phones of Khashoggi’s family, likely by agents of the United Arab Emirates, a close Saudi ally. Several received malicious texts that infected their phones with Pegasus, a tool created by the NSO Group to remotely access a target’s microphone, text messages, and location.
Qahtani, who briefly faced house arrest, was swiftly cleared of wrongdoing in Khashoggi’s death by the Saudi government. Five of the hitmen in the squad sent to kill Khashoggi were sentenced to death, including Maher Abdulaziz Mutreb, an intelligence officer who worked under Qahtani. Qahtani’s current relationship with the institute is unknown. People hold posters of slain Saudi journalist Jamal Khashoggi, near the Saudi Arabia consulate in Istanbul, on Oct. 2, 2020.

Following Khashoggi’s killing, many U.S. firms faced pressure to exit business deals with Saudi entities. Yet, in the years following Khashoggi’s murder, the Saudi cyberwarfare institute central to the plot has continued to do business with Western defense industry leaders.
In 2019, BAE Systems, a major defense contractor based in the U.S. and the U.K., entered into a training agreement with the MBS College of Cyber Security. Last year, Cisco unveiled a training relationship with the Saudi Federation of Cybersecurity, Programming, and Drones.
BAE, reached for comment, distanced itself from the deal. “BAE Systems works with a number of partner companies based in Saudi Arabia,” said a spokesperson for the company. “ISE, one of our Saudi partner companies, was awarded a contract in 2019 by the MBS College for Cyber Security to provide support services to establish the college, such as general staffing and facilities management but this contract wasn’t activated and is still on hold.”
Alexander has continued to do work in the region as a member of Amazon’s board. Intelligence Online, a trade outlet for intelligence contractors, reported, “As a partner of Amazon, for which it offers native surveillance of its AWS’ cloud traffic, IronNet helps the company win public contracts, especially since CEO Keith Alexander has sat on Amazon’s board.”
IronNet, however, has faltered in recent months, with two waves of layoffs this year and a lawsuit from investors. The company has touted skyrocketing growth, like many defense-related contractors, by promising to harness growing security threats. Much of the American traditional defense industry has long sought lucrative foreign relationships, particularly with the Saudi government, a path IronNet appears to have attempted to follow.
And President Joe Biden, who promised during his election campaign to make the Saudi state a “pariah” over the slaying, has since appeared to move on from the scandal. In June, he traveled to Riyadh to shore up the U.S.-Saudi alliance and request an increase in oil production. The four-year anniversary of Khashoggi’s slaying is on October 2.
IT’S EVEN WORSE THAN WE THOUGHT.
What we’re seeing right now from Donald Trump is a full-on authoritarian takeover of the U.S. government.
This is not hyperbole.
Court orders are being ignored. MAGA loyalists have been put in charge of the military and federal law enforcement agencies. The Department of Government Efficiency has stripped Congress of its power of the purse. News outlets that challenge Trump have been banished or put under investigation.
Yet far too many are still covering Trump’s assault on democracy like politics as usual, with flattering headlines describing Trump as “unconventional,” “testing the boundaries,” and “aggressively flexing power.”
The Intercept has long covered authoritarian governments, billionaire oligarchs, and backsliding democracies around the world. We understand the challenge we face in Trump and the vital importance of press freedom in defending democracy.
We’re independent of corporate interests. Will you help us?
IT’S BEEN A DEVASTATING year for journalism — the worst in modern U.S. history.
We have a president with utter contempt for truth aggressively using the government’s full powers to dismantle the free press. Corporate news outlets have cowered, becoming accessories in Trump’s project to create a post-truth America. Right-wing billionaires have pounced, buying up media organizations and rebuilding the information environment to their liking.
In this most perilous moment for democracy, The Intercept is fighting back. But to do so effectively, we need to grow.
That’s where you come in. Will you help us expand our reporting capacity in time to hit the ground running in 2026?
We’re independent of corporate interests. Will you help us?

I’M BEN MUESSIG, The Intercept’s editor-in-chief. It’s been a devastating year for journalism — the worst in modern U.S. history.
We have a president with utter contempt for truth aggressively using the government’s full powers to dismantle the free press. Corporate news outlets have cowered, becoming accessories in Trump’s project to create a post-truth America. Right-wing billionaires have pounced, buying up media organizations and rebuilding the information environment to their liking.
In this most perilous moment for democracy, The Intercept is fighting back. But to do so effectively, we need to grow.
That’s where you come in. Will you help us expand our reporting capacity in time to hit the ground running in 2026?
We’re independent of corporate interests. Will you help us?
Latest Stories

Daughter of 2028 Olympics Chair Dreams of Competing in LA — for Israel
Hollywood scion Casey Wasserman faced criticisms as Los Angeles Olympics chief for his connections to the late pedophile Jeffrey Epstein.

Anthropic Says We Must Stop Authoritarian AI. But What About Its Authoritarian Investors?
Anthropic wants to keep AI away from repressive regimes. But what about its part-owner, the repressive dictatorship of Abu Dhabi?
The Intercept Briefing
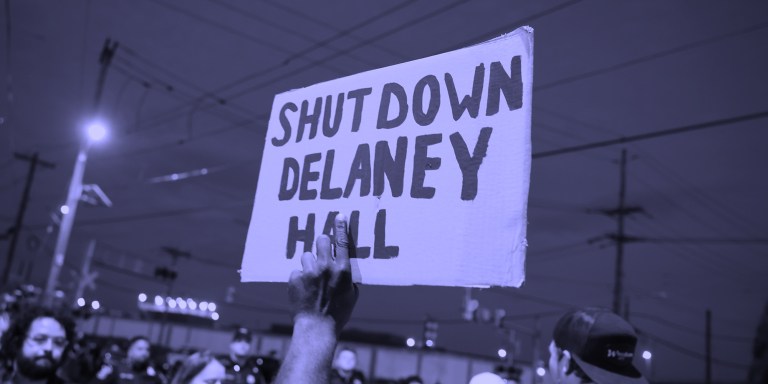
“Warehousing Human Beings”
Former immigration judge Andrea Sáenz and American Immigration Council’s Aaron Reichlin-Melnick on the conditions at Delaney Hall and other ICE detention centers across the U.S.









