For the fourth time since 2007, an internal audit shows the Department of Homeland Security isn’t deactivating access cards in the hands of ex-employees, leaving its secure facilities vulnerable to intruders.
A new report by Homeland Security’s Office of Inspector General shows that the department is systemically failing to revoke tens of thousands of “personal identity verification” cards that allow staff to enter sensitive, secure facilities and access internal data networks, despite being warned about the problem for 15 years. The issue is made worse, the report continues, by the fact that Homeland Security’s internal record-keeping is so shoddy that it was impossible to determine how many ex-staffers have working access cards they aren’t supposed to.
“DHS has not prioritized ensuring that PIV cards are terminated when individuals no longer require access.”
Like many modern office workers, Homeland Security hands out office-unlocking keycards to its employees to make sure strangers can’t wander in off the street. And, like most workplaces, the department is supposed to follow a standard policy: When an employee is no longer an employee, for whatever reason, their card is to be promptly deactivated.
Unlike most employers, though, Homeland Security is a component of the U.S. Intelligence Community, meaning these credit card-sized badges have a “grave potential for misuse if lost, stolen, or compromised,” according to the inspector general report. Unfortunately for the department — and potentially the homeland — the OIG’s latest audit found that’s exactly what’s happening, and on a vast scale.
“DHS has not prioritized ensuring that PIV cards are terminated when individuals no longer require access,” the report says. “Without effective PIV card and security clearance management and monitoring, DHS cannot ensure only authorized individuals have access to its controlled electronic systems and facilities.”
The December 20 report — based on interviews and firsthand analysis of the internal database Homeland Security is supposed to use to track its active personal identity verification cards and associated owners — says the department failed to deactivate nearly half of the cards it was supposed to within the recommended 18-hour window after termination. Some PIV cards remained improperly active for months, and over 36,000 may not have been deactivated at all. Those with cards that remain improperly activated include employees who were fired, retired, failed background checks, or died.
While the cards also grant holders access to sensitive DHS data networks, the department claimed to the inspector general that the electronic network access keys embedded in the cards were deactivated, “preventing access to electronic systems.”
On the PIV cards, the report’s conclusion is blunt: “We determined that unauthorized individuals could gain access to Department facilities.”
The inspector general report found that Homeland Security’s failure to secure its borders was caused by a widespread disregard for its own rules.
After being scolded for this exact same problem for the past 15 years, the department developed an array of software systems and procedures to catalog PIV ownership and revocation — which on paper would grant the department an instant bird’s-eye view of who has improper access to its facilities. The inspector general report, however, found the department still fails to use these systems and, when it does, they don’t really work.
Despite the perennial nature of the access problem, compliance appears to have failed at the most basic level: “The revocation delays occurred because DHS did not have an adequate mechanism to ensure managers promptly notified security officials when cardholders separated from the Department,” the report reads.
“Some DHS officials also told us they intentionally did not enter a revocation date after revoking PIV cards.”
Department personnel told auditors the Identity Management System, which Homeland Security is supposed to use to track card status, has a serious flaw: “Some DHS officials also told us they intentionally did not enter a revocation date after revoking PIV cards because doing so caused reports to become too large, resulting in IDMS slowing down.”
Given that the software used to track access card revocation apparently can’t track access card revocation without “slowing down,” the report notes, “it was impossible for DHS OIG to conclusively determine if DHS officials revoked PIV card access promptly or at all.”
The auditors also found that Homeland Security may not have withdrawn employee security clearances, as required, for its over 53,000 former employees since 2021, again because the department isn’t using an internal database meant to track such activity.
With the card and security clearance revocation issues taken together, the auditors identified a distinct threat — albeit somewhat muddled, owing to bad bookkeeping: “As a result, there is a risk that individuals who no longer require access to systems and facilities could circumvent controls and enter DHS buildings and controlled areas.”
According to the report, the department disagrees with the Office of the Inspector General as to the magnitude of the problem, but not that the problem exists. In a response published in the report, the department says it will implement a series of reforms and improved record-keeping polices to make sure cards are deactivated when they’re supposed to be — just as it promised after a 2018 audit flagged the very same failures.
IT’S EVEN WORSE THAN WE THOUGHT.
What we’re seeing right now from Donald Trump is a full-on authoritarian takeover of the U.S. government.
This is not hyperbole.
Court orders are being ignored. MAGA loyalists have been put in charge of the military and federal law enforcement agencies. The Department of Government Efficiency has stripped Congress of its power of the purse. News outlets that challenge Trump have been banished or put under investigation.
Yet far too many are still covering Trump’s assault on democracy like politics as usual, with flattering headlines describing Trump as “unconventional,” “testing the boundaries,” and “aggressively flexing power.”
The Intercept has long covered authoritarian governments, billionaire oligarchs, and backsliding democracies around the world. We understand the challenge we face in Trump and the vital importance of press freedom in defending democracy.
We’re independent of corporate interests. Will you help us?
IT’S BEEN A DEVASTATING year for journalism — the worst in modern U.S. history.
We have a president with utter contempt for truth aggressively using the government’s full powers to dismantle the free press. Corporate news outlets have cowered, becoming accessories in Trump’s project to create a post-truth America. Right-wing billionaires have pounced, buying up media organizations and rebuilding the information environment to their liking.
In this most perilous moment for democracy, The Intercept is fighting back. But to do so effectively, we need to grow.
That’s where you come in. Will you help us expand our reporting capacity in time to hit the ground running in 2026?
We’re independent of corporate interests. Will you help us?

I’M BEN MUESSIG, The Intercept’s editor-in-chief. It’s been a devastating year for journalism — the worst in modern U.S. history.
We have a president with utter contempt for truth aggressively using the government’s full powers to dismantle the free press. Corporate news outlets have cowered, becoming accessories in Trump’s project to create a post-truth America. Right-wing billionaires have pounced, buying up media organizations and rebuilding the information environment to their liking.
In this most perilous moment for democracy, The Intercept is fighting back. But to do so effectively, we need to grow.
That’s where you come in. Will you help us expand our reporting capacity in time to hit the ground running in 2026?
We’re independent of corporate interests. Will you help us?
Latest Stories
The Intercept Briefing
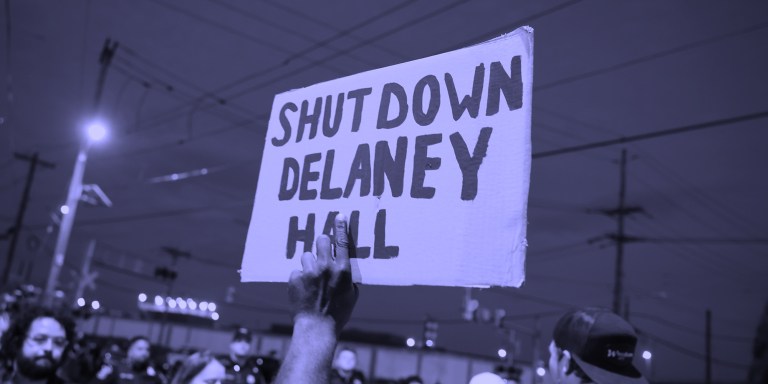
“Warehousing Human Beings”
Former immigration judge Andrea Sáenz and American Immigration Council’s Aaron Reichlin-Melnick on the conditions at Delaney Hall and other ICE detention centers across the U.S.

Trump Administration Tries to Shift Blame for Ebola Response
After cutting its support for frontline healthcare workers in Central Africa, the Trump administration is pointing fingers.

Israel’s Lebanon Blitz
House Dems Coming Around on Iran War — But Won’t Vote to Stop Israel’s Destruction of Lebanon
Though its backers remain optimistic, a bill blocking U.S. support for Israel’s war in Lebanon exposed rifts among Democrats.









